IT Security Assessment / Audit
ITSec Ltd follows a proven risk-based IT Assessment / Audit methodology to help with the identification, evaluation of IT security risks and thereby improve the overall IT Security level. This structured approach ensures planning of tasks and availability of subject matter experts as and when required so as to complete the scope within the budgeted cost and timelines.
The IT system within any company has different dimensions and with various levels of operation. An IT assessment helps to identify the strengths and weaknesses of your IT system, and also provides solutions that enhance efficiency, productivity, and profitability. This process is quite complicated, therefore the need for a specialists who help with the assessment.
When you assess the information technology (IT) of your business it reduces the costs of solving IT issues that impact your network, data security, and other factors in general.
The following will give you more insight into what an IT Security Assessment / Audit is, the benefits of assessing your IT systems, and other related issues.
Implementing the Right IT Security Assessment / Audit
During an IT assessment process, a range of options related to your business must be considered.
An assessment assesses all factors in your IT department that contributes to your daily successes. Some of these factors include individuals, and policies. These factors must be aligned with your business needs both its short- and long-term goals.
IT assessment proffers an adequate solution to the following:
ITSec Ltd uses a combination of standards like ISO 27001/27002, 22301 for applying best practices for the security process and technical frameworks and benchmarks like COBIT to test and benchmark key technical infrastructure security controls. The steps followed in the IT Assessment process are given below:
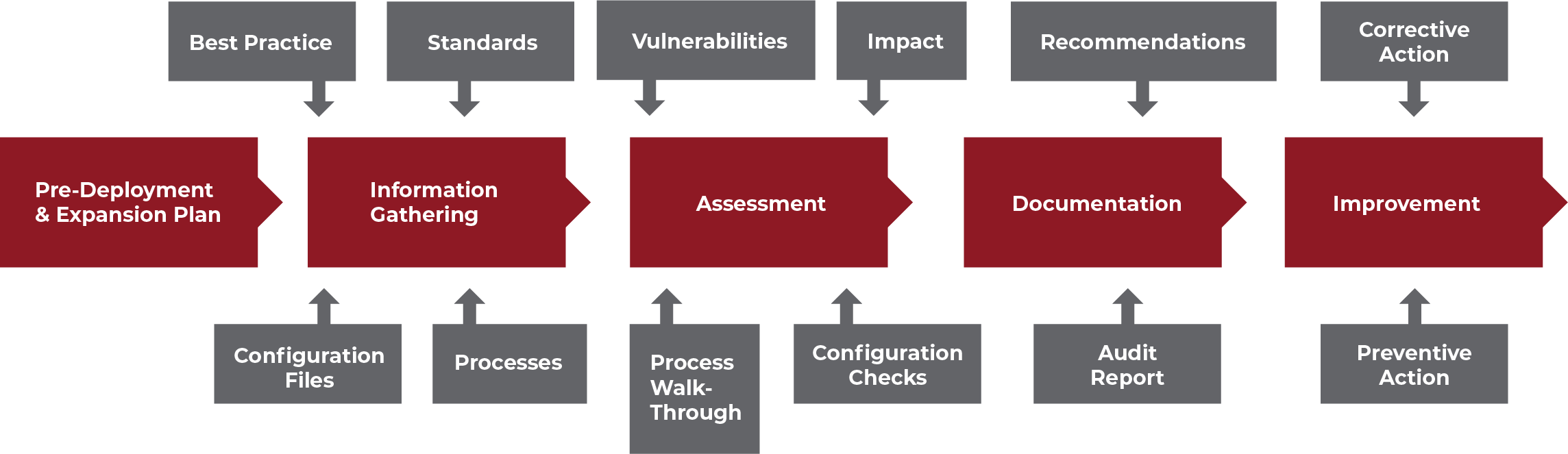
What does an IT Security Assessment / Audit process look like?
Every assessment focuses on various IT and business aspects, some assessments include:
Benefits of an IT Security Assessment / Audit
IT systems require adequate management in order to ensure efficiency at all levels. A number of benefits are associated with implementing the right IT assessment, some of these benefits include:
Let Us accompany you